社区微信群开通啦,扫一扫抢先加入社区官方微信群

社区微信群
社区微信群开通啦,扫一扫抢先加入社区官方微信群

社区微信群
下图展示了数字证书(HTTPS中使用的由CA签名的公钥证书)的签名和验证原理: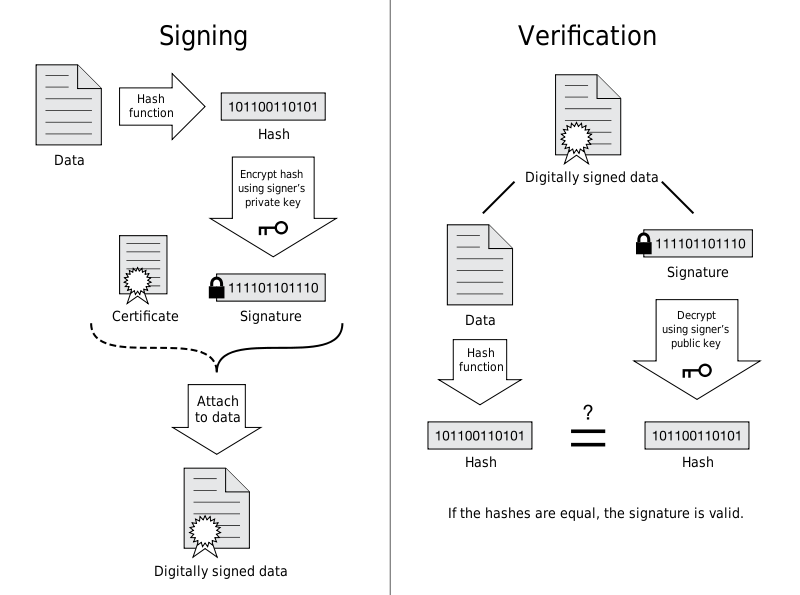
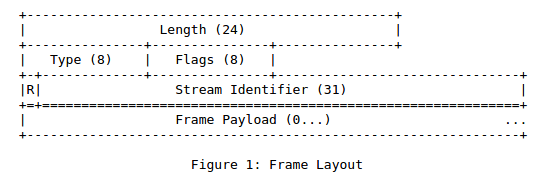
下图是HTTP2 Frame 格式:RFC7540 - Hypertext Transfer Protocol Version 2 (HTTP/2)

$ cd /usr/local/nginx/conf $ openssl genrsa -des3 -out server.key 1024 #建议:2048 $ openssl req -new -key server.key -out server.csr #证书签名请求(CSR) $ cp server.key server.key.org $ openssl rsa -in server.key.org -out server.key $ openssl x509 -req -days 365 -in server.csr -signkey server.key -out server.crt #证书签名
worker_processes 1;
server {
server_name YOUR_DOMAINNAME_HERE;
listen 443 ssl http2;# http2 is available only since OpenSSL version 1.0.2
listen 80;
if ($scheme = http) {
rewrite ^(.*)$ https://$server_name$1 permanent;
}
ssl_certificate server.crt;
ssl_certificate_key server.key;
keepalive_timeout 70;
}
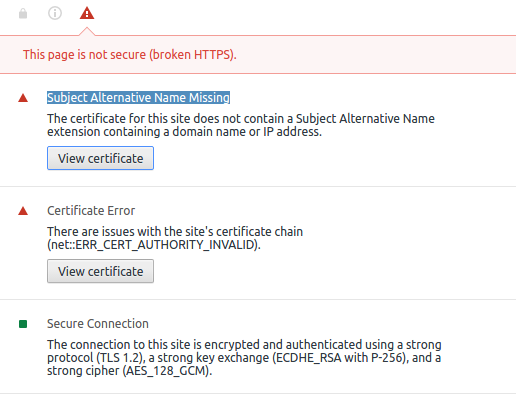
另外,本人在Chromium 58.0.3029.110 和 Firefox 53.0.3 下均证实了HTTP2被成功启用:

if you have a chain certificate file (sometimes called an intermediate certificate) you don't specify it separately like you do in Apache. Instead you need to add the information from the chain cert to the end of your main certificate file. This can be done by typing "cat chain.crt >> mysite.com.crt" on the command line. Once that is done you won't use the chain cert file for anything else, you just point Nginx to the main certificate file
下图展示了证书链的工作原理:
syntax:ssl [on|off]
default:ssl off
context:main, server
syntax:ssl_certificate file
default:ssl_certificate cert.pem
context:main, server
syntax:ssl_certificate_key file
default:ssl_certificate_key cert.pem
context:main, server
syntax:ssl_client_certificate file
default:none
context:main, server
syntax: ssl_dhparam file
default: none
context: main, server
syntax: ssl_ciphers file
default: ssl_ciphers ALL:!ADH:RC4+RSA:+HIGH:+MEDIUM:+LOW:+SSLv2:+EXP
context: main, server
ssl_ciphers ALL:!ADH:!EXPORT56:RC4+RSA:+HIGH:+MEDIUM:+LOW:+SSLv2:+EXP;
Complete list can be looked with the following command:
openssl ciphers
syntax: ssl_prefer_server_ciphers [on|off]
default: ssl_prefer_server_ciphers off
context: main, server
syntax: ssl_protocols [SSLv2] [SSLv3] [TLSv1]
default: ssl_protocols SSLv2 SSLv3 TLSv1
context: main, server
syntax:ssl_session_cache off|none|builtin:size and/or shared:name:size
default:ssl_session_cache off
context:main, server
ssl_session_cache builtin:1000 shared:SSL:10m;
syntax:ssl_session_timeout time
default:ssl_session_timeout 5m
context:main, server
如果觉得我的文章对您有用,请随意打赏。你的支持将鼓励我继续创作!
